The shift to hybrid and remote work brings new challenges for data protection and e-waste – but with the right plan, you can keep sensitive information safe and your business compliant. Here’s what every company needs to know to stay secure and sustainable.
When employees work from home, company-owned devices containing sensitive data are no longer within the secure perimeter of the office. This creates a complex web of logistical and security issues when it comes to data destruction.
How do you securely retrieve and destroy data on devices scattered across countless home offices? Without a clear strategy, your company is exposed to data breaches, compliance violations, and logistical nightmares.
Our guide will walk you through the complexities of data destruction for a remote workforce and provide a clear, secure solution.
Understanding Device Management Models and Their Challenges
When an employee leaves the company or their equipment is due for an upgrade, the devices in their possession – laptops, hard drives, and mobile phones – often remain in closets or home offices, quietly increasing your company’s data security risk.
Today’s remote and hybrid work forces often use a mix of device management models, each with their own security and data destruction challenges:
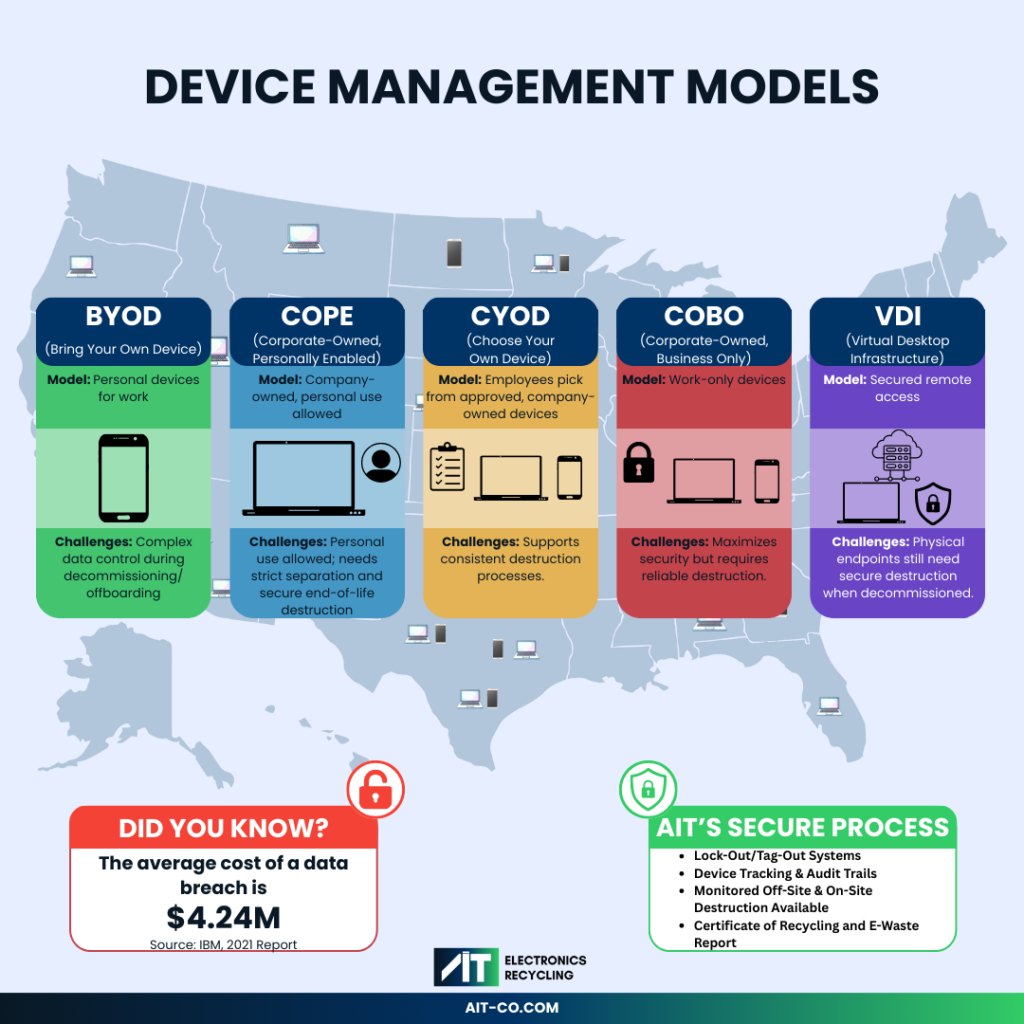
- BYOD (Bring Your Own Device): Employees use their personal devices for work, making data control complex when it’s time to decommission or offboard.
- COPE (Corporate-Owned, Personally Enabled): The company owns the device but allows personal use, requiring strict separation and secure data destruction at end of life.
- CYOD (Choose Your Own Device): Employees select from a list of approved, company-owned devices, supporting a consistent destruction process.
- COBO (Corporate-Owned, Business Only): Devices are issued strictly for work, maximizing security and compliance but still requiring trustworthy destruction.
- Virtual Desktop Infrastructure (VDI): Employees access a secured remote work environment from any device; however, if physical endpoints (like thin clients or laptops) are decommissioned, secure destruction is still necessary.
A decentralized workforce means your sensitive data is stored in dozens, or even hundreds of different locations. This lack of centralized control makes it incredibly difficult to track and manage the lifecycle of each device. When equipment is forgotten or improperly handled, the risk of a data breach skyrockets.
🔒 Did You Know?
• Nearly 40% of data breaches are caused by lost or stolen devices.
• A single data breach can cost a company an average of $4.24 million.
• Improperly disposed devices can retain recoverable data, even after a factory reset.
Learn more about AIT’s NIST 800-88 and NAID certified data destruction services here.
The Logistical Nightmare of Asset Recovery
By preparing an asset list before distributing devices, companies can easily track which assets are returned and which are outstanding, increasing visibility and control throughout the recovery process. Still, individual shipments from home directly to a recycling facility increase the risk of lost or damaged devices and make it harder to track assets, raising the chance of data exposure.

Centralizing e-waste collection to a single location prior to pickup from a certified recycler streamlines coordination, reduces the risk of loss or damage, and ensures all devices are accounted for and securely prepared for data destruction.
📦 Remote Collection Reality
• Nearly 60% of organizations report major delays, lost devices, or data security gaps when trying to recover IT assets from remote employees.
• Each unreturned device not only risks sensitive data exposure, but also adds to audit and inventory headaches for IT teams.
• A decentralized retrieval process magnifies these risks, making secure tracking and end-to-end accountability absolutely essential.
How AIT Can Help:
Electronics recycling with AIT ensures every device is tracked, accounted for, and fully destroyed through certified processes. We maintain a complete chain of custody with locked containers in transit, documented asset tracking, and provide a Certificate of Destruction for auditable proof.
Contact us now to help you with your nationwide e-waste recycling collection and data destruction today!
Learn more about our IT asset disposition (ITAD) services.
Ensuring Compliance in a Remote World
Data protection regulations like HIPAA, FACTA, and GDPR don’t make exceptions for remote work. Your company remains responsible for protecting sensitive data, regardless of where that data resides. Improper disposal of a single device from a home office can lead to severe non-compliance penalties, including hefty fines and legal action.

Proving that your company followed compliant data destruction procedures for remote assets is crucial during an audit. Without a certified process, you leave your business exposed to significant financial and reputational damage. Simply asking an employee to wipe a device or have it destroyed at an e-waste recycling facility is not enough to meet these stringent legal standards.
⚖️ Compliance is Non-Negotiable
• Fines for non-compliance with e-waste and data privacy laws can reach tens of thousands of dollars per violation.
• Regulations require auditable proof of data destruction, which employee-led efforts cannot provide.
• Partnering with a certified vendor like AIT ensures that you meet all legal requirements for e-waste handling and data security, remaining compliant with R2v3, e-Stewards and ISO 14001 industry standards.
Discover how AIT’s regulatory compliance assurance can protect your business.
The Environmental Impact of Improper Disposal
When employees are left to dispose of company electronics on their own, these devices often end up in local landfills. E-waste contains hazardous materials like lead, mercury, and cadmium, which can leach into soil and groundwater, causing significant environmental and health harm.

A sustainable IT asset disposition program is a key component of any modern corporate social responsibility (CSR) strategy. By ensuring that your remote workforce’s e-waste is properly recycled, you protect the environment and enhance your company’s reputation and trust.
♻️ E-Waste by the Numbers
• E-waste represents only 2% of trash in landfills but equals 70% of overall toxic waste.
• Recycling one million laptops saves the energy equivalent to the electricity used by 3,657 U.S. homes in a year.
• A certified recycling partner guarantees that hazardous materials are managed safely and valuable resources are recovered.
Learn more about AIT’s R2, e-Stewards and ISO 14001 compliant e-waste recycling services.
Secure Your Remote Workforce with AIT
Managing data destruction for a hybrid or remote workforce doesn’t have to be a source of risk and complexity. With a strategic approach and the right partner, you can implement a secure, compliant, and efficient process that protects your business from every angle.
AIT delivers complete, centrally managed solutions designed for today’s distributed workforce. We help you track your asset inventory with our asset tracking services and guide you in centralizing e-waste collection at your facility. From there, you can schedule a pickup so your devices will be directly transported to our facility for recycling and destruction. Or, choose on-site or monitored data destruction for increased security.
Whatever the challenge, AIT’s R2-compliant recycling, robust asset tracking, certified data destruction, and audit-ready documentation services turn remote IT asset disposition into a streamlined and secure process that you can trust.
Ready to secure your team’s remote IT assets? Contact AIT today for a customized solution that ensures your data remains protected, no matter where your team is located across the nation.